Have you noticed how internet search is changing?
As long as I can remember, search worked by feeding it a few keywords or a question and it would return back thousands, or even hundreds of thousands of results. These results were prioritized by custom algorithms that take in multiple factors to prioritize them to direct you to a website for more information.
This is what most of us think of when we refer to “Googling” something. It is akin to the idea of going into a library and asking the librarian where to find a specific section of books. It didn’t lead to any direct answers, just a pointer to shelves full of books that we would then spend time searching through to find the answer we wanted.
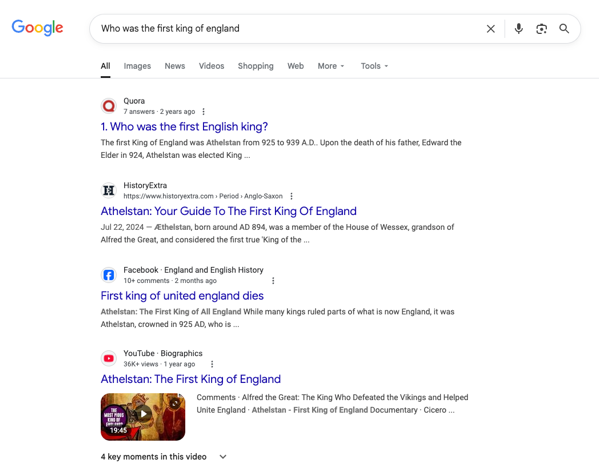
As AI has started to take hold, I have seen how it has been embedded into our internet searches. This was a pretty cool enhancement in that the search engine would put together a simple response to your request in summary. I don’t know the statistics of it, but I am really interested to know how many searches end here, and the user never needs to click into one of the reference links.
This became more of a hybrid approach where it would give you a quick answer, but then provide a list of results like before to continue searching the book shelves for the answer you wanted.
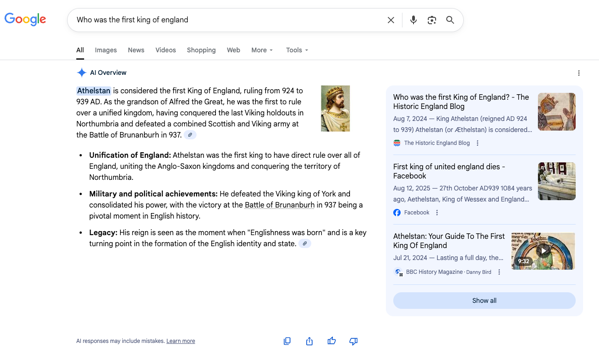
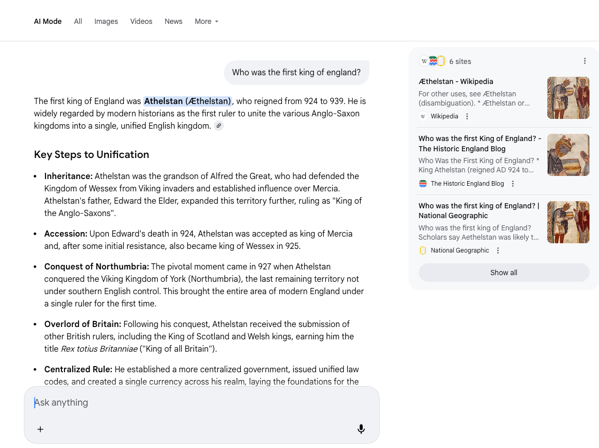
Google’s new AI Mode takes it to the next step of a conversation. At this level, it is like you are holding a conversation with a guru of any subject. You are able to ask questions to get the answers. If the answer wasn’t quite right, you could change your question to get more specific. You keep asking questions until the response is acceptable. You will still see a list of references, related to the answer, but you won’t get hundreds of links. Think of it as if the guru gives you an answer and also provides a list of the books he used to get it. This is helpful because you may want more context or to even verify for yourself that the guru is correct.
Why do I bring this up? There was an interesting discussion on the Down the Security Rabbithole podcast, Episode 671 – It’s the End of the Internet As We Know It, that this was mentioned.
The discussion really got me thinking about how search is changing and the effects it has on the internet as a whole. I want to talk about two examples.
Effect on critical thinking
The advancement of how we search for information is absolutely amazing. The speed that we are able to find the answer to most questions has improved our ability to our jobs, grow our knowledge and help advance key research for things like technology, medicine, etc. The time it would have taken to look something up in a book was long when we were going to the library or digging through our collection of encyclopedias. I am amazed every day at the information that is available to my kids that I could have only dreamed of growing up.
I must consider the cost as well. Without guardrails in place, how do we ensure that people are still able to think critically about a problem? The results we are seeing come back from these search results can be pretty good, but they can also be pretty bad. How do people know when to believe the answer, or when to question it and dig deeper to verify the results?
The longer we go just taking the default answer from a search engine’s AI system, the further we get from spending cycles verifying the answers on our own.
These systems are getting better, but I am sure will always have their faults or build their own biases. What happens when a person asks what is 2+2 and the system returns 5? 20 years ago, I would have believed every person would question that based on their fundamental education. Today, in 2025, I believe there are people that would take this answer as fact without a question at all.
As time goes on, and people turn to Googling everything, at some point we lose that fundamental knowledge. We stop learning how to do simple addition because “why waste my time on that, when I can just ask ChatGPT?”.
Another example I give on the podcast is around cooking recipes. Have you ever just Googled how to make something simple, like chocolate chip cookies? With the new results we get from AI searches, they will just spit out a recipe. Sure, there might be some links to actual cooking sites, but why not just take the initial AI answer?
Do you know enough about food ingredients to trust the answer provided? What happens when the ingredients include something that is actually dangerous to humans? Would you know not to use that and question the recipe?
There are real world consequences to this.
Don’t get me wrong, there are similar consequences to you just following the recommendations on some random cooking site, or that influencer’s TikTok channel.
Ad Revenue
The other thing I find interesting is around ad revenue that powers both search engines and the organizations behind the links you click during historic searches. Search is free because they are making money through the ads payed by many of those links displayed and clicked. How will this affect the search providers when links are no longer displayed or they are not clicked because the AI answer was enough?
This question actually takes me back up to the pervious section where I discussed consumers just taking the AI answer and not digging deeper. What happens when the answers are biased by the target companies buying the promotions? Does this end up distorting the answers toward paid bias, and if so, how long does it take before one can easily sway the world to start believing something that just isn’t true? It just seems true because enough money was put into it to make it the theme of the answer. Then add to it that people no longer perform critical thinking and just take the answer as fact.
On the organization side, the side that pays for their ads to be in the search results, what effect do we see? If the consumer is just interacting with a bot and no links are displayed, you lose the visibility you once had. The chances of someone just finding you from a simple search decreases and less traffic may come to your site. Maybe there is some path that this tactic changes to be part of the AI results somehow, but that gets us back into the bias in those results if they are driven by sponsors.
It could just be that marketing has left search results behind. Maybe organizations have solved this through the use of social media channels. Maybe we will see commercials or ad banners start appearing in the AI chat bots.
Final Thoughts
It is an interesting time when we think about internet search offerings and how they are changing. Change isn’t always bad and the positive value in this case may outweigh the negatives. Our ability to get to answers more quickly has a lot of positive value to advancing a lot of things. However, there are some negatives that just need to be considered. We need to make sure that the responses provided are accurate and unbiased as to not start retraining our knowledge on inaccurate information. A small shift in our understandings can have a huge ripple effect years down the road.